Go to Top
Go to Top
Identify vulnerabilities that could lead to data leaks from the attacker’s perspective,
and strengthen your security posture in advance.
Identify vulnerabilities that could lead to data leaks from the attacker’s perspective, and strengthen your security posture in advance.
Identify vulnerabilities that could lead to data leaks from the attacker’s perspective,and strengthen your security posture in advance.
The choice of security-first
enterprises: Enki WhiteHat.
The choice of security-first
enterprises: Enki WhiteHat.
With extensive project experience across industries,
we provide customized security solutions tailored to your business environment and needs.
With extensive project experience across industries,
we provide customized security solutions tailored to your business environment and needs.
With extensive project experience across industries, we provide customized security solutions tailored to your business environment and needs.

Financial Institutions

Large Enterprises

IT & Security Companies

Military / Public Sector Organizations

Public

National Defense










Financial Institutions

Large Enterprises

IT & Security Companies

Military / Public Sector Organizations

Public

National Defense









Unidentified hacks and relentless breaches
uncertainty keeps building up, while the burden of responsibility falls entirely on security teams.
uncertainty keeps building up, while the burden of responsibility falls entirely on security teams.
uncertainty keeps building up, while the burden of responsibility falls entirely on security teams.
With data breaches continuing to occur, is your company truly safe?
With data breaches continuing to occur, is your company truly safe?
With data breaches continuing to occur, is your company truly safe?
Uncontrolled IT Assets
Uncontrolled IT Assets
Sophisticated Attacks
Sophisticated Attacks
Frequent Feature Updates
Frequent Feature Updates
Increasing Vendor Connections
Increasing Vendor Connections
Cloud & Remote Work
Cloud & Remote Work
AI Service Adoption
AI Service Adoption
Shortage of Security Personnel
Shortage of Security Personnel
Stricter Regulatory Requirements
Stricter Regulatory Requirements
Stay one step ahead of attackers.
Stay one step ahead of attackers.
Stay one step ahead of attackers.
Stay one step ahead of attackers.
Stay one step ahead of attackers.
Stay one step ahead of attackers.
Enterprise security must be meticulous.
Attackers exploit even the smallest 1% of blind sots— It’s time to think like them,
and adopt proactive, preventive security measures.
Enterprise security must be meticulous.
Attackers exploit even the smallest 1% of blind sots— It’s time to think like them,
and adopt proactive, preventive security measures.
Enterprise security must be meticulous.
Attackers exploit even the smallest 1% of blind sots— It’s time to think like them,
and adopt proactive, preventive security measures.
We uncover critical vulnerabilities that threaten your enterprise.
We uncover critical vulnerabilities that threaten your enterprise.
We uncover critical vulnerabilities that threaten your enterprise.
Ethical white-hat hackers simulate attacks from the attacker’s perspective to
identify issues that could lead to financial loss, data breaches, or service disruptions.
Ethical white-hat hackers simulate attacks from the attacker’s perspective to
identify issues that could lead to financial loss, data breaches, or service disruptions.
Ethical white-hat hackers simulate attacks from the attacker’s perspective toidentify issues that could lead to financial loss, data breaches, or service disruptions.
Server Takeover &
Privilege Escalation
Server Takeover &
Privilege Escalation

Validate potential for root-level server access remotely
Validate potential for root-level server access remotely
Identify server takeover scenarios via unused ports and vulnerable services
Identify server takeover scenarios via unused ports and vulnerable services
Detect internal server access paths through service vulnerability analysis
Detect internal server access paths through service vulnerability analysis
Malicious Activity
Malicious Activity

Simulate duplication of e-currency/points and fraudulent payments
Simulate duplication of e-currency/points and fraudulent payments
Prove feasibility of creating and distributing malicious apps
Prove feasibility of creating and distributing malicious apps
Validate privilege escalation through vulnerabilities (XSS, data exposure, etc.)
Validate privilege escalation through vulnerabilities (XSS, data exposure, etc.)
Verify potential bypass routes via external staff/employee devices
Verify potential bypass routes via external staff/employee devices
Data Exfiltration
Data Exfiltration

Confirm risk of sensitive data leaks (customer PII, internal documents, etc.)
Confirm risk of sensitive data leaks (customer PII, internal documents, etc.)
Demonstrate external data exfiltration via arbitrary command execution
Demonstrate external data exfiltration via arbitrary command execution
Validate customer data access after admin privilege hijacking
Validate customer data access after admin privilege hijacking
Assess data extraction risks from bypassing existing security solutions
Assess data extraction risks from bypassing existing security solutions
Reproduce external data transmission via SSH tunneling scenarios
Reproduce external data transmission via SSH tunneling scenarios
Enki Products
Enki Products
OFFen
OFFen
OFFen
No more waiting,
Vulnerability assessments
No more waiting,
Vulnerability assessments
more
more
ASM
ASM
ASM
Visualize every hidden threat in your asset network—no blind spots.
Visualize every hidden threat in your asset network—no blind spots.

Checklist/Offensive PT
Checklist/Offensive PT
Checklist/Offensive PT
Optimized for ISMS-P certification
Assess only what you need—specific websites, apps, or systems
Optimized for ISMS-P certification
Assess only what you need—specific websites, apps, or systems

Red Team
Red Team
Red Team
End-to-End security assessments by professional white-hat hackers through real-world attack scenarios
End-to-End security assessments by professional white-hat hackers through real-world attack scenarios

Enki Products
Enki Products
CAMP
CAMP
CAMP
A security capability growth platform that enhances your team’s practical skills and strengthens internal response—even in critical moments.
A security capability growth platform that enhances your team’s practical skills and strengthens internal response—even in critical moments.
more
more
Training
Training
Training

Build solid security capabilities from the ground up through practice-driven learning in digital forensics, incident response, malware analysis, web hacking, and security device operations.
Build solid security capabilities from the ground up through practice-driven learning in digital forensics, incident response, malware analysis, web hacking, and security device operations.
Wargame
Wargame
Wargame

Strengthen core skills by solving domain-specific challenges, share high-quality write-ups, and boost motivation with a ranking system.
Strengthen core skills by solving domain-specific challenges, share high-quality write-ups, and boost motivation with a ranking system.
CTF (Capture the Flag)
CTF (Capture the Flag)
CTF (Capture the Flag)

Easily set up in-house CTF environments using diverse content—even for non-specialists—and assess team-wide security capabilities.
Easily set up in-house CTF environments using diverse content—even for non-specialists—and assess team-wide security capabilities.
Attack-Defense Exercises
Attack-Defense Exercises
Attack-Defense Exercises

Strengthen organizational collaboration with real-time attack and defense drills in a virtual infrastructure that mirrors the enterprise environment, using real-world cases (TTPs, vulnerabilities, scenarios).
Strengthen organizational collaboration with real-time attack and defense drills in a virtual infrastructure that mirrors the enterprise environment, using real-world cases (TTPs, vulnerabilities, scenarios).
Enki Service
Enki Service

Offensive Security Assessments
Experienced white-hat hackers with advanced technical expertise conduct comprehensive assessments across your IT infrastructure. They identify and validate threats that could lead to financial loss, data breaches, or service disruptions, and provide actionable defense strategies.
more

Red Teaming

Compliance Audits

Penetration Testing

Remediation Checks

Cyber Threat Intelligence
Backed by the analysis of over 20,000 malware samples from North Korea, China, Russia, and beyond, our experts deliver refined threat intelligence and tailored response strategies. During incidents, we trace attacker behaviors, infiltration paths, and impact scope to eliminate root causes and strengthen defenses.
more

Malware Analysis

Digital Forensics

Security Training & Exercises
As Korea’s #1 cyber defense competition operator, we provide high-quality, real-world challenges that simulate actual incidents. With extensive penetration testing and global competition experience, we deliver the latest cybersecurity training and customized practice environments designed to equip professionals with immediately applicable skills.
more

Hands-on Training

CTF Operations

Phishing Simulations

Offensive Security Assessments
Experienced white-hat hackers with advanced technical expertise conduct comprehensive assessments across your IT infrastructure. They identify and validate threats that could lead to financial loss, data breaches, or service disruptions, and provide actionable defense strategies.
more

Red Teaming

Compliance Audits

Penetration Testing

Remediation Checks

Cyber Threat Intelligence
Backed by the analysis of over 20,000 malware samples from North Korea, China, Russia, and beyond, our experts deliver refined threat intelligence and tailored response strategies. During incidents, we trace attacker behaviors, infiltration paths, and impact scope to eliminate root causes and strengthen defenses.
more

Malware Analysis

Digital Forensics

Security Training & Exercises
As Korea’s #1 cyber defense competition operator, we provide high-quality, real-world challenges that simulate actual incidents. With extensive penetration testing and global competition experience, we deliver the latest cybersecurity training and customized practice environments designed to equip professionals with immediately applicable skills.
more

Hands-on Training

CTF Operations

Phishing Simulations
Check out the latest
threat insights and reports.
more
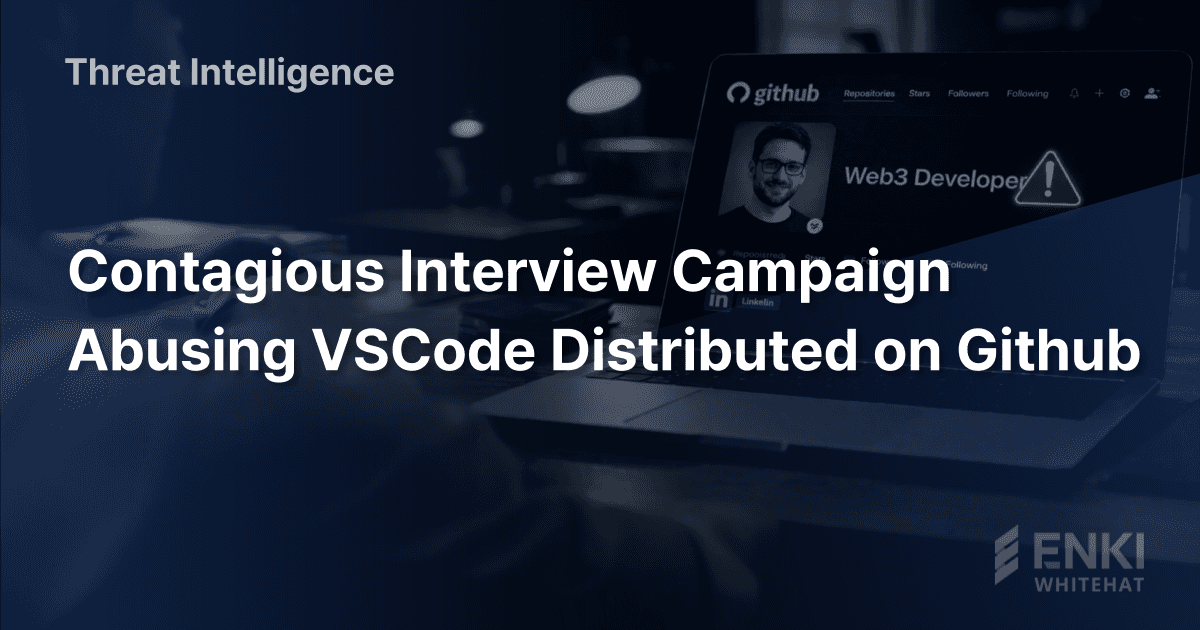
Threat Intelligence
Contagious Interview Campaign Abusing VSCode Distributed on Github
We recently identified multiple instances of malware on Github that abuse VS Code automation features. Our analysis attributes this activity to Contagious Interview, a DPRK-nexus campaign active since at least 2025-08 that primarily targets developers.In this campaign, threat actors typically pose as recruiters to approach targets. Under the guise of coding tests or video interviews, they lure victims into downloading malicious payloads such as BeaverTail, InvisibleFerret, and OtterCookie.The Github accounts identified in this investigation purported to be recruiters for legitimate companies, Web3 developers, and fictitious organizations. The threat actors likely employed these personas to blend in with normal recruitment and development activities, establishing trust to facilitate malware distribution.Furthermore, our analysis of the deployed malware revealed artifacts suggesting the code was generated using LLMs. This indicates that the threat actors are actively using AI technologies to develop malicious tools more efficiently and complicate reverse engineering efforts.This report examines the threat actors' Github activities and details the operational mechanisms and capabilities of the malware used in these attacks.

ENKI WhiteHat
Feb 27, 2026
Threat Intelligence
Contagious Interview Campaign Abusing VSCode Distributed on Github
We recently identified multiple instances of malware on Github that abuse VS Code automation features. Our analysis attributes this activity to Contagious Interview, a DPRK-nexus campaign active since at least 2025-08 that primarily targets developers.In this campaign, threat actors typically pose as recruiters to approach targets. Under the guise of coding tests or video interviews, they lure victims into downloading malicious payloads such as BeaverTail, InvisibleFerret, and OtterCookie.The Github accounts identified in this investigation purported to be recruiters for legitimate companies, Web3 developers, and fictitious organizations. The threat actors likely employed these personas to blend in with normal recruitment and development activities, establishing trust to facilitate malware distribution.Furthermore, our analysis of the deployed malware revealed artifacts suggesting the code was generated using LLMs. This indicates that the threat actors are actively using AI technologies to develop malicious tools more efficiently and complicate reverse engineering efforts.This report examines the threat actors' Github activities and details the operational mechanisms and capabilities of the malware used in these attacks.

ENKI WhiteHat
Feb 27, 2026

Threat Intelligence
EtherRAT Targeting Windows Disguised as a Game Mod Installer
EtherRAT is a JavaScript-based implant first documented by Sysdig. The malware was originally observed targeting Linux environments via the React2Shell vulnerability (CVE-2025-55182).During our analysis of EtherRAT, we obtained multiple MSI files communicating with the malware’s C&C server. Our analysis confirmed the existence of EtherRAT variants targeting Windows. Notably, some files were distributed within archive files masquerading as installers for game mods.This report details the analysis of the Windows-based EtherRAT variant disguised as a game mod installer and examines the associated smart contract infrastructure.

EnkiWhiteHat
Jan 20, 2026

Threat Intelligence
EtherRAT Targeting Windows Disguised as a Game Mod Installer
EtherRAT is a JavaScript-based implant first documented by Sysdig. The malware was originally observed targeting Linux environments via the React2Shell vulnerability (CVE-2025-55182).During our analysis of EtherRAT, we obtained multiple MSI files communicating with the malware’s C&C server. Our analysis confirmed the existence of EtherRAT variants targeting Windows. Notably, some files were distributed within archive files masquerading as installers for game mods.This report details the analysis of the Windows-based EtherRAT variant disguised as a game mod installer and examines the associated smart contract infrastructure.

EnkiWhiteHat
Jan 20, 2026

Threat Intelligence
Kimsuky Distributing Malicious Mobile App via QR Code
In September 2025, the ENKI WhiteHat Threat Research Team detected a malicious mobile application distributed via phishing websites. The threat actor leveraged QR codes and notification pop-ups to lure victims into installing and executing the malware on their mobile devices.Our analysis confirms this sample as the latest iteration of "DOCSWAP," a malware strain originally named by S2W in March 2025. While this version retains the behavioral patterns of earlier variants, it implements a distinct internal APK decryption mechanism. Additionally, we uncovered multiple indicators connecting this activity to the DPRK-nexus threat actor, Kimsuky.Leveraging APK metadata and infrastructure overlaps, we identified three additional malicious applications and seven C&C servers. The threat actor designed each application with distinct decoy themes to deceive victims and evade suspicion.

EnkiWhiteHat
Dec 16, 2025

Threat Intelligence
Kimsuky Distributing Malicious Mobile App via QR Code
In September 2025, the ENKI WhiteHat Threat Research Team detected a malicious mobile application distributed via phishing websites. The threat actor leveraged QR codes and notification pop-ups to lure victims into installing and executing the malware on their mobile devices.Our analysis confirms this sample as the latest iteration of "DOCSWAP," a malware strain originally named by S2W in March 2025. While this version retains the behavioral patterns of earlier variants, it implements a distinct internal APK decryption mechanism. Additionally, we uncovered multiple indicators connecting this activity to the DPRK-nexus threat actor, Kimsuky.Leveraging APK metadata and infrastructure overlaps, we identified three additional malicious applications and seven C&C servers. The threat actor designed each application with distinct decoy themes to deceive victims and evade suspicion.

EnkiWhiteHat
Dec 16, 2025
Press
Press

Are you ready to begin building worry-free tomorrow security?
Step into a safer tomorrow with confidence

Are you ready to begin building worry-free tomorrow security?
Step into a safer tomorrow with confidence

Are you ready to begin building worry-free tomorrow security?