


Beyond One-Time Testing, Moving Towards Continuous Verification
In August 2021, attackers first infiltrated SK Telecom's internal network. They installed malware on multiple servers, and SK Telecom became aware of the breach on April 18, 2025.
According to the investigations by the government and the Personal Information Protection Commission, the attacker stayed inside for over three years, expanding their foothold, and eventually leaked user information externally in April 2025.
The biggest lesson from this incident is clear. The fact that the clock of attacks and the clock of security checks no longer move at the same speed.
Thus, questions regarding security are changing now.
It’s no longer about 'Have you done a penetration test?' but rather, 'Are you continuously verifying at the speed of attacks?'
An annual check-up is close to just a snapshot of a past moment. Meanwhile, systems change, external connection points increase, and attackers find new routes.
The era of constant penetration testing does not mean randomly probing all systems every day, but rather creating a system where verification continues uninterrupted around key assets.
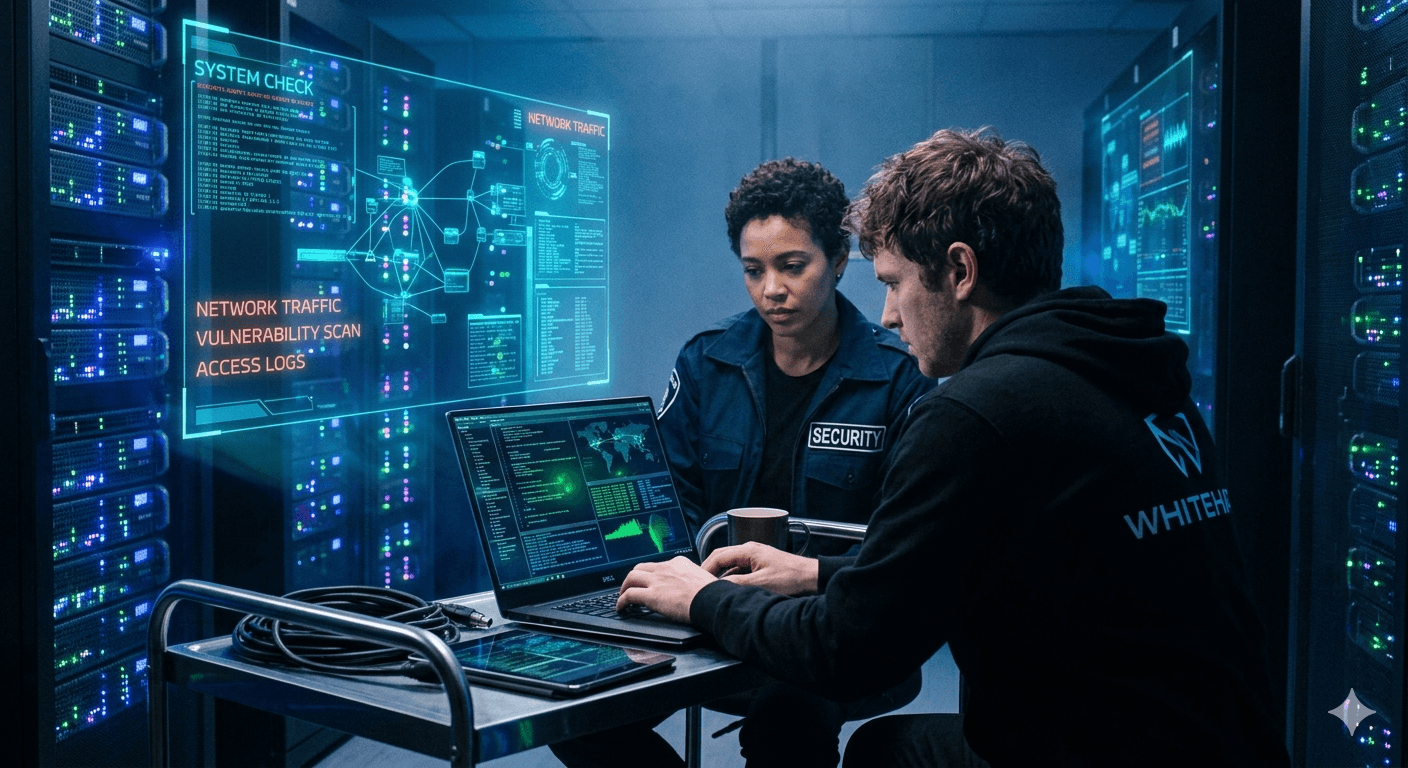
caption - In the era of constant penetration testing, collaboration with experts using automated tools is necessary. (Produced by Jaeminai)
First, government regulations are changing in this direction.
In their October 2025 comprehensive cybersecurity strategy, the government announced plans to inspect over 1,600 IT systems across public, financial, and telecommunications sectors with massive+continuous checks and to establish a constant inspection system using mock hacking exercises and white hackers.
Particularly for telecom companies, they plan to execute high-intensity surprise inspections using actual hacking methods. The Financial Services Commission also announced that starting September of the same year, it will conduct blind mock hacking across the entire financial sector as part of a strategy to prevent the recurrence of breaches.
One-time penetration tests have clear limitations.
First, they are predictable. When tests are conducted in a prepared state on a scheduled date, it is difficult to fully reveal an attacker's detours, operational errors, or misuse of privileges.
Second, they show only a snapshot of that day. As assets, accounts, and exposure to external threats continuously change, the report captures only that moment.
Third, the cycle of discovery and remediation can easily break. If vulnerabilities are not fixed and re-verified in a loop, the security level cannot be maintained for long. This is why the government has introduced surprise inspections, and financial authorities have opted for blind mock hacking.
Abroad, the era of constant penetration tests began quite a while ago.
The USA's CISA CDM (Continuous Diagnostics and Mitigation) program is a system for continuously diagnosing and mitigating federal agencies' security statuses.
The European Central Bank has aligned with the 2025 ‘Threat Intelligence-Based Ethical Red Team Test Europe Framework (TIBER-EU)’ and the standards required by the EU’s 'Digital Operational Resilience Act (DORA)' for ‘Threat-Led Penetration Testing (TLPT)’.
In simple terms, these improvements aim to test financial companies more realistically based on actual threat intelligence. The Bank of England also ensures that financial companies assess their security controls through scenarios similar to actual attacks via the ‘CBEST’ (Critical National Infrastructure Banking Supervision and Evaluation Testing) framework and ‘STAR-FS’ (Simulated Targeted Attack and Response for Financial Services). Although the names differ, the direction is the same. We are moving away from annual evaluations to a system of ongoing verification against actual threats.
Regulatory Changes in Korea
Regulation/System Name | Applicable Targets | Key Requirements | Inspection Cycle |
|---|---|---|---|
Comprehensive Government Information Security Measures | About 1,650 core IT systems in public, financial, and communication sectors (officially announced as over 1,600) | Immediate security checks for 288 public institutions, 152 administrative agencies, 261 financial companies, and 949 ISMS certified companies. Unscheduled checks using real hacking methods for telecommunication companies. Establish ongoing inspection system with mock hacking training and use of white hackers. Switch ISMS·ISMS-P focus to field inspections and pursue certification cancellation for major flaws | Continuous + Immediate Thorough Inspection |
Financial Sector Accident Recurrence Prevention Measures | Entire Finance Sector | Prepared after the SGI Seoul Guarantee accident in July 2025. Self-inspection by the entire financial sector, field inspections by the Financial Supervisory Service, and joint blind mock hacking by the Financial Supervisory Service and the Financial Security Institute starting in September. Reinforcement of ransomware response, backup systems, and hacking defense systems | Immediate Implementation from September 2025 |
Blind Mock Hacking Training in Financial Sector | Entire Financial Sector (Banks, Insurance, Securities, Savings Banks, Cooperative Finance, Electronic Finance Companies, etc.) | Unscheduled training without prior notice of the attack time and target companies. The RED IRIS team of the Financial Security Institute checks server penetration and DDoS response capabilities. Expanded implementation across all sectors from September 4 to October 31, 2025 | Concentrated Implementation for 2 Months in 2025 |
Vulnerability Analysis and Evaluation of Electronic Financial Infrastructure | 178 Financial Companies (as of 2026) | Operated through comprehensive inspections, standalone inspections, and checks of publicly accessible websites. Expanded 2026 evaluation criteria to 869 items in 15 fields. Expanding scope of inspections to mobile apps, cloud, websites, etc. | Once a Year |
Global big tech companies already conduct constant vulnerability verification as a standard.
Since 2014, Google has operated a dedicated research group called Project Zero, dedicating researchers' time 100% to discovering vulnerabilities and structurally improving security. In 2024 alone, Google awarded nearly $12 million in rewards to over 600 researchers worldwide through its vulnerability reward program. It also operates separate bug bounty programs related to generative AI, receiving over 150 reports.
Microsoft has been running an AI red team since 2018. In 2025, through its bug bounty program, it awarded $17 million, working with external researchers to enhance vulnerability discovery. Through ‘Zero Day Quest’, it concentrated on finding high-risk vulnerabilities in cloud and AI fields, and the ‘Secure Future Initiative’ report disclosed that 180 new vulnerabilities were preemptively discovered and addressed in this process.
AI is further accelerating the speed of cyber attacks.
In its threat intelligence report in August 2025, Anthropic revealed that Claude Code is used to automate reconnaissance, credential collection, and network infiltration, and has been exploited in data exfiltration campaigns against several international organizations.
The report included cases of less skilled attackers developing and selling ransomware with AI assistance. An additional evaluation in January 2026 indicated that the current Claude model has reached a level capable of conducting multi-stage attacks using only standard open source tools on networks of dozens of devices.
AI is not magic that creates hacking anew but serves as an accelerator that lowers the thresholds and increases the speed of preparing for and executing attacks.
In such an environment, the defensive approach must change. Continuous penetration testing is not about shaking every system daily.
First, you must always keep high-risk targets such as systems exposed externally, critical data, authentication frameworks, and partner connection segments up-to-date. Over this, you must layer regular penetration tests, blind tests, red teams, and bug bounties.
And the most crucial final step is post-action re-verification. It shouldn't end with finding but should be a loop of finding, fixing, and re-confirming.
Of course, it's not feasible for every company to have a dedicated red team. To have an organization that continuously designs attack scenarios, finds vulnerabilities, and conducts re-verifications like Google or Microsoft, you need manpower, budget, and operational experience. Especially for companies with fewer dedicated security personnel, small and medium enterprises, and companies rapidly operating services, it's challenging to create such a system alone.
However, abandoning continuous verification is not an option. A practical alternative in such cases is utilizing external experts and Penetration Testing as a Service (PTaaS). Continuous penetration testing isn't complete with only people or tools.
(Image)
Automated tools excel at broad, frequent checks. They can quickly scan areas needing frequent checks, such as asset changes, external exposure status, basic vulnerabilities, and repetitive verification. Meanwhile, expert staff are strong at delving deep. They identify bypass routes from an attacker's viewpoint, verify actual penetration possibilities by linking multiple weaknesses, and find issues needing contextual understanding like business logic loopholes or authorization misuse. Simply put, tools look broadly, while experts look deeply. For a continuous verification system to function properly, both must work in tandem.
It's about performing penetration testing with expert help as needed and not ending with a single report but continuing with repeated checks and re-verification. Even companies unable to maintain a large internal red team can utilize external expertise to create an operating model close to a continuous verification system.
The key is not the organizational form but the continuity of verification. If internal capabilities are lacking, it's more realistic and effective to use experts and services to maintain an unbroken loop of inspection-action-re-verification.

Popular Articles







