In 2026, as AI technology has surged, hacking techniques have become more sophisticated, and government security policies are changing rapidly as well. In particular, if you are a security manager at a small or medium-sized business with limited staff and budget, that burden will likely feel even greater.
This article introduces the key direction of current government security policies you need to know now, the five attack routes most often used in real red team projects, and how SMEs can use government subsidies to prevent security incidents.
3 Government Policies to Watch in 2026
Three recent policy changes point in the same direction.
"Precisely identify externally exposed assets, and prove through continuous checks that they cannot be breached even in real hacking attempts."
N2SF (National Network Security Framework) activation (View details)
The government is moving from the existing uniform network-separation policy to N2SF (National Network Security Framework), which applies differentiated security based on data sensitivity. With AI and cloud adoption causing the attack surface to expand explosively, field-tested verification—not just controls on paper—must back it up.
Implementation of a Korean-style security vulnerability reporting/remediation/disclosure system (CVD/VDP) (View details)
Starting in the second half of this year, the government will pilot CVD/VDP, allowing white-hat hackers to report vulnerabilities without legal burden. This means corporate security must move beyond internal checks to a 24/7 continuous inspection system with outside experts.
Mandatory information security disclosure (View details)
From 2027, information security disclosure will be mandatory for all listed companies, and the effectiveness will be strengthened by fully applying 'real penetration tests' to ISMS-P certification, which had stopped at a formal checklist.
Enki White Hat Red Team Top 5 Attack Routes
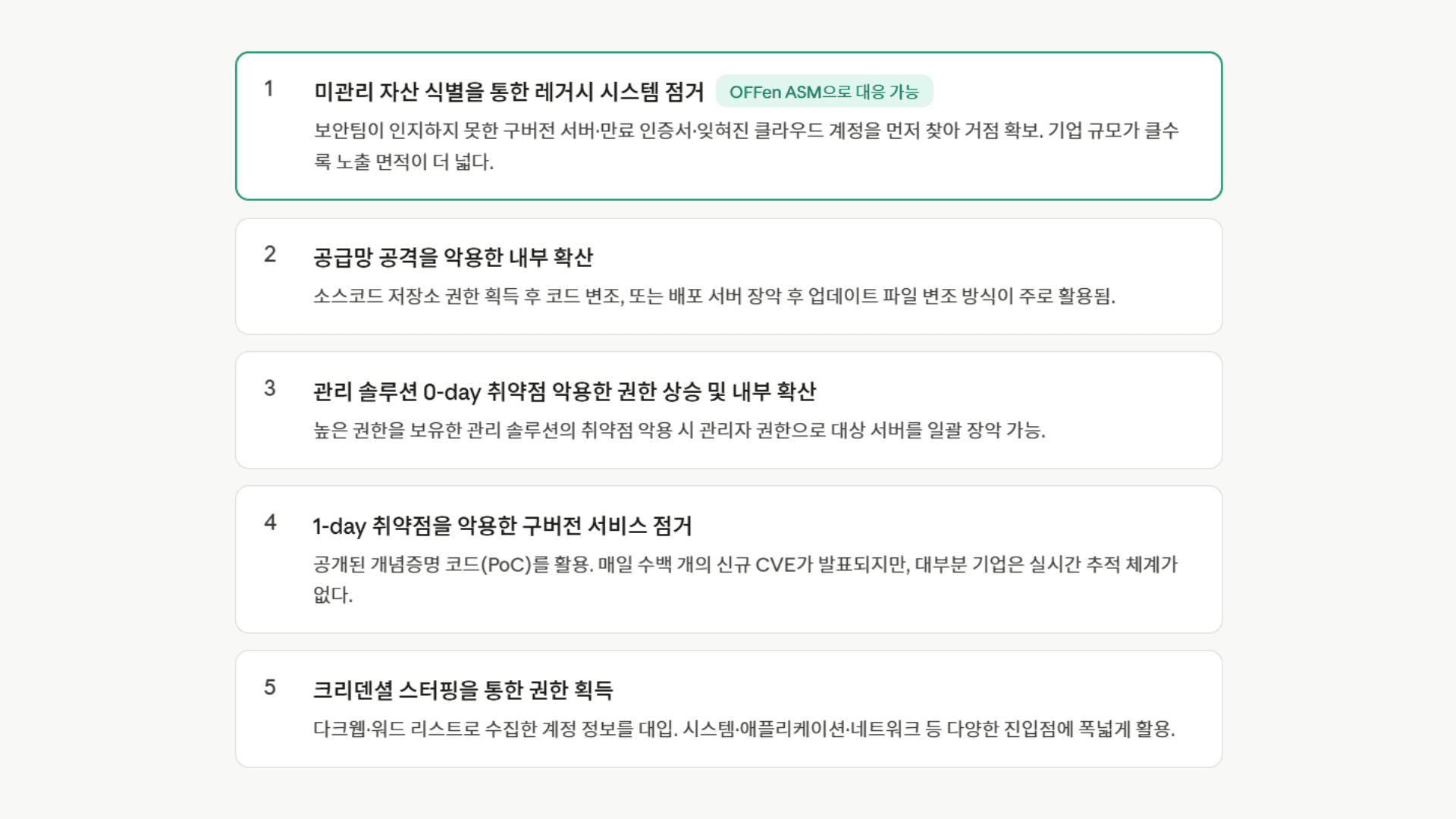
Analyzing the data from red team projects conducted by ENKI Whitehat in 2024, the most effective attack route ranked No. 1 was 'seizing legacy systems by identifying unmanaged assets.'
As a company’s IT environment grows, old test servers, cloud accounts left behind after the owner has departed, and outdated services whose updates have stopped are neglected. Since these are assets even the security team doesn’t know about, naturally no one patches them, making them the easiest entry point for attackers.
Legacy system takeover through identifying unmanaged assets : Infiltration via old test servers and abandoned old websites unknown even to the security team
Internal spread by exploiting a supply chain attack : Compromise source code repositories or deployment servers and insert malware into update files
Privilege escalation and internal spread by exploiting a management solution 0-day vulnerability : Steal privileges by exploiting undisclosed vulnerabilities in the solution installed to manage servers
Taking over outdated services by exploiting a 1-day vulnerability : Target outdated services for which patches are already available, but only our company has not updated
Gaining privileges through credential stuffing : Seize administrator accounts by randomly entering account information leaked on the dark web, etc.
What is notable is that these attack routes are organically connected. Unmanaged assets become a foothold and lead to internal spread (No. 2), and unpatched services become prey to 1-day vulnerabilities (No. 4). A single unmanaged asset creates a structure that leads to a domino-like chain of compromise.
OFFen ASM: Attack surface management for finding vulnerable domains
Enki White Hat directly witnessed over 10 years through penetration testing projects the impact of poor IT asset management, and developed the attack surface management service OFFen ASM to address it.
Unlike post-incident response solutions such as EDR and SIEM, OFFen ASM is a proactive attack surface management service that first finds all entry points an attacker can exploit before an incident occurs. Another differentiator of OFFen ASM is that the know-how of white hat hackers with the No. 1 share in operating domestic hacking defense competitions and DEF CON championship experience is built into the scan engine itself.
OFFen ASM Core Features
1. '24/7 Automated Detection Without Load' Starting from a Single Domain
Just enter one representative domain of the company, and it automatically tracks all connected IT assets. You can split collections by asset priority and configure scans, and it thoroughly identifies Shadow IT, open APIs, expired SSL certificates, and even IoT devices. Applying distributed scanning technology that does not burden production servers even when running scans across many assets, it builds a 365-day always-on monitoring system without worrying about service interruptions.
2. 'Asset Safety Rating' distilled from Enki Whitehat's know-how
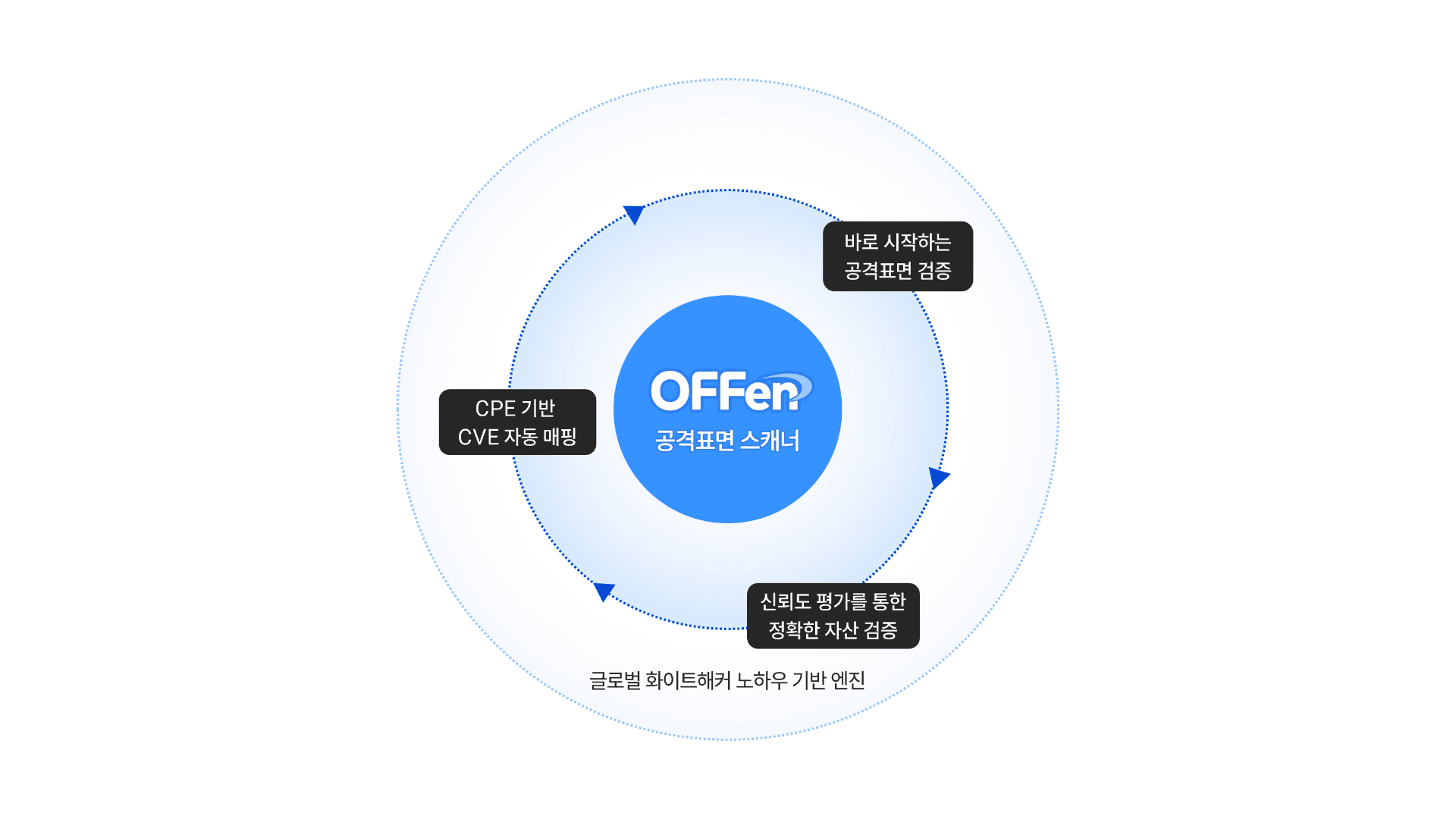
It evaluates importance by comparing each subdomain found based on the main domain against Enki Whitehat's vast project execution data.
Data-based scoring: It scores assets by combining their purpose, exposure level, and security configuration status.
Safety grade assignment: Based on the calculated score, it provides an intuitive safety grade so that both executives and practitioners can grasp the security level at a glance.
3. 'Priority Targets' selected based on trustworthiness & risk
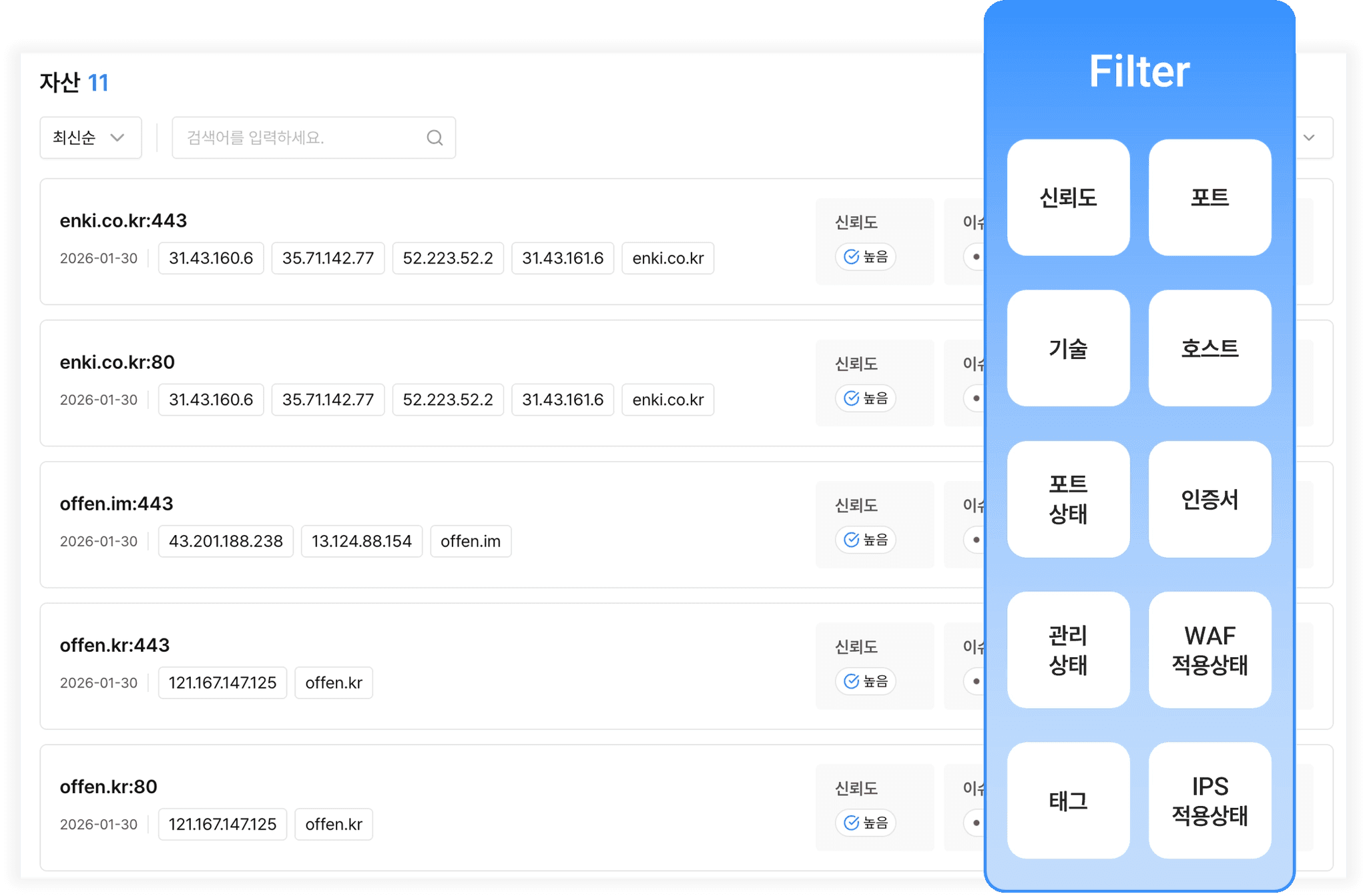
OFFen ASM uses its own evaluation metrics to score the probability that a detected asset truly belongs to our company (trustworthiness), resulting in high accuracy. In other words, it blocks situations where unrelated assets trigger false positives. It also comprehensively quantifies the technical difficulty of vulnerabilities, their impact on confidentiality and integrity, and their real-world exploitability (such as whether a public exploit exists), providing prioritization data so you can see only the risks that need immediate action now. Managers do not need to sift through hundreds of alerts; they only need to focus on the few 'core threats' pointed out by OFFen ASM.
Risky Asset Use Case Requiring Management
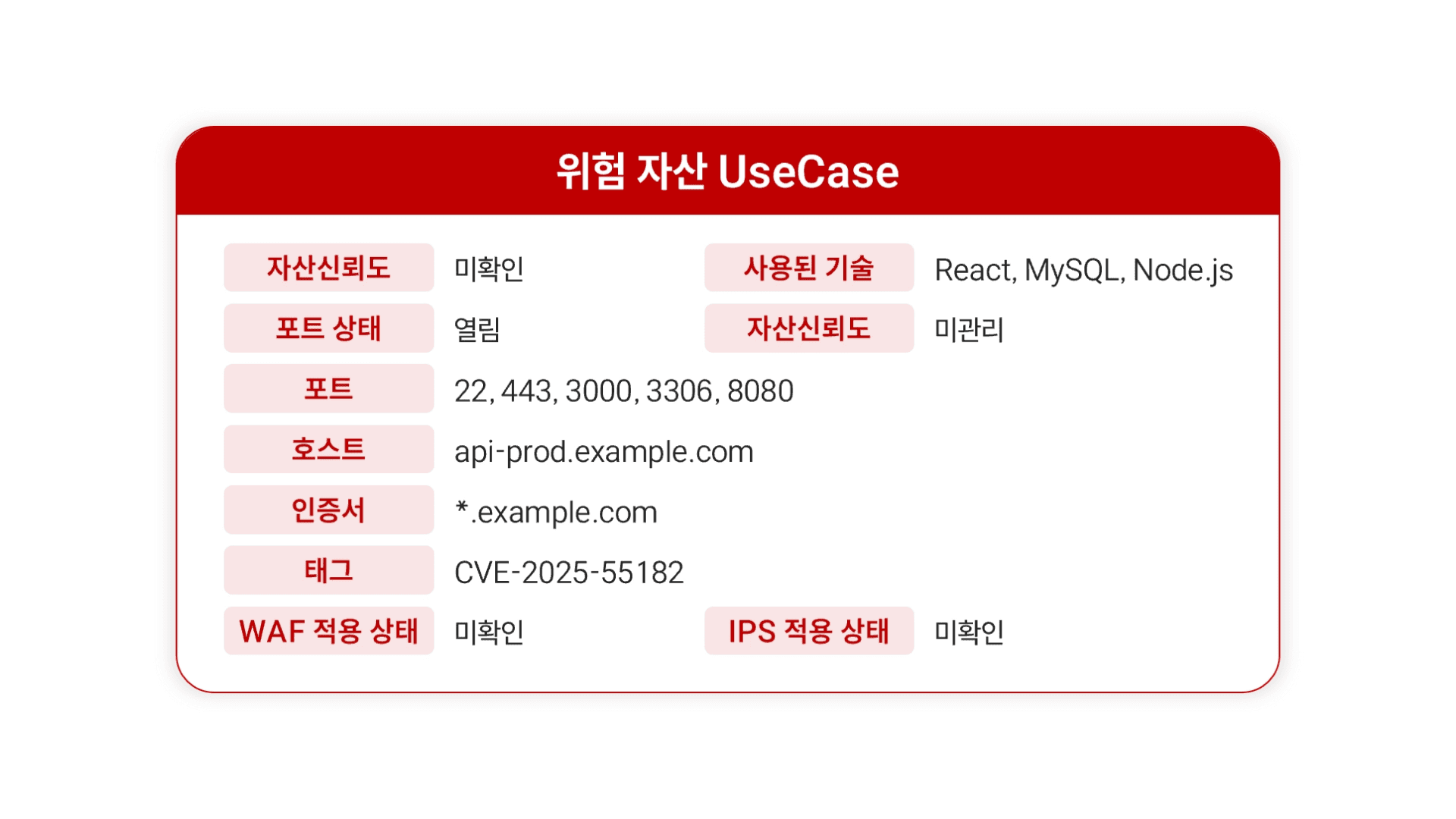
Asset trustworthiness: Unverified
Port status: Open
Ports: 22, 443, 3000, 3306, 8080
Host: api-prod.example.com
Certificate: *.example.com
Tag: CVE-2025-55182
WAF status: Unverified
Used technologies: React, MySQL, Node.js
Asset trustworthiness: Unmanaged
IPS status: Unverified
Safe Asset Use Case
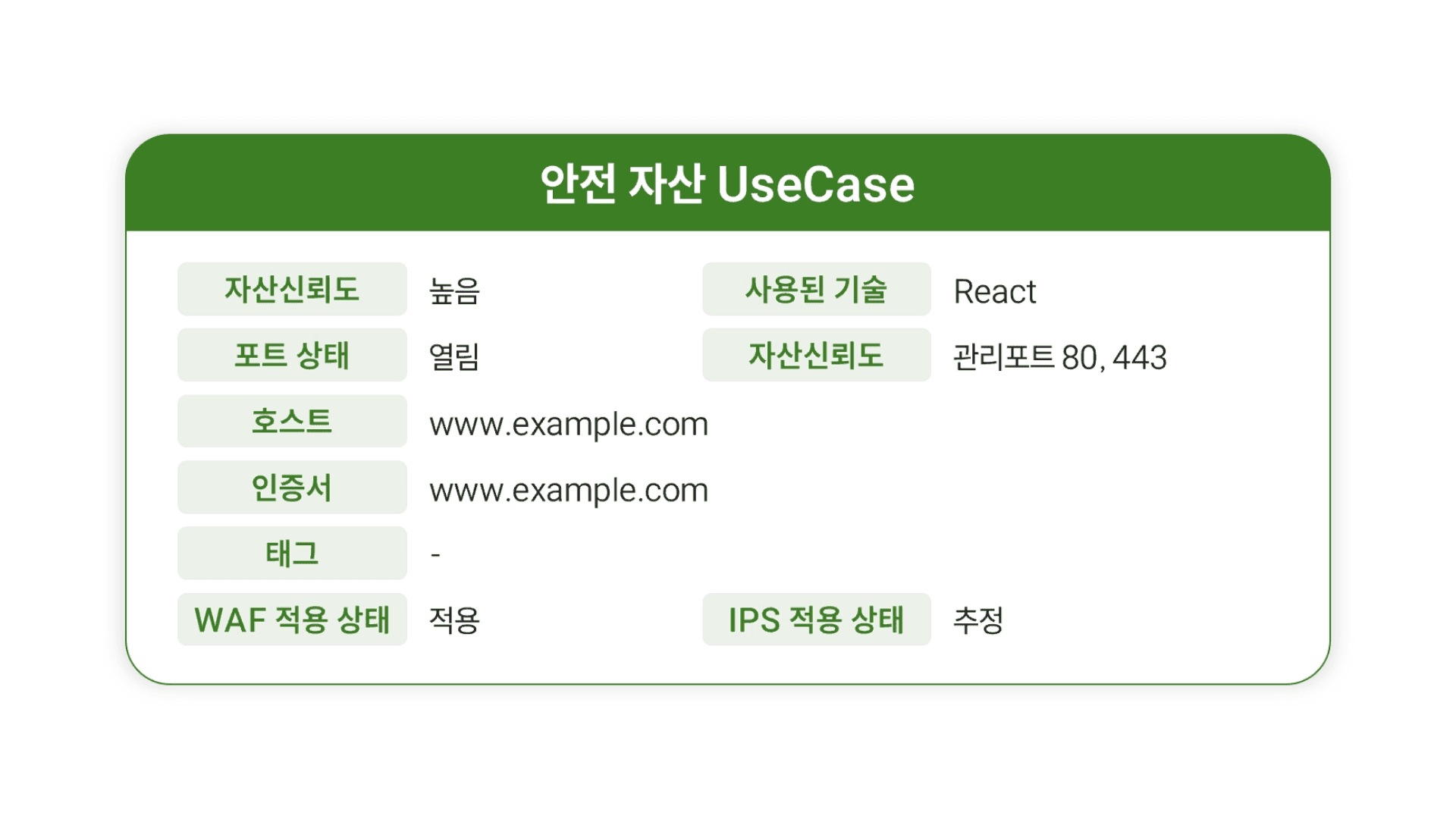
Asset trustworthiness: High
Port status: Open
Host: www.example.com
Certificate: www.example.com
Tag: -
WAF status: Applied
Used technologies: React
Asset trustworthiness: Managed ports 80, 443
IPS status: Suspected
4. 'Network Map' that lets you gauge threat impact at a glance
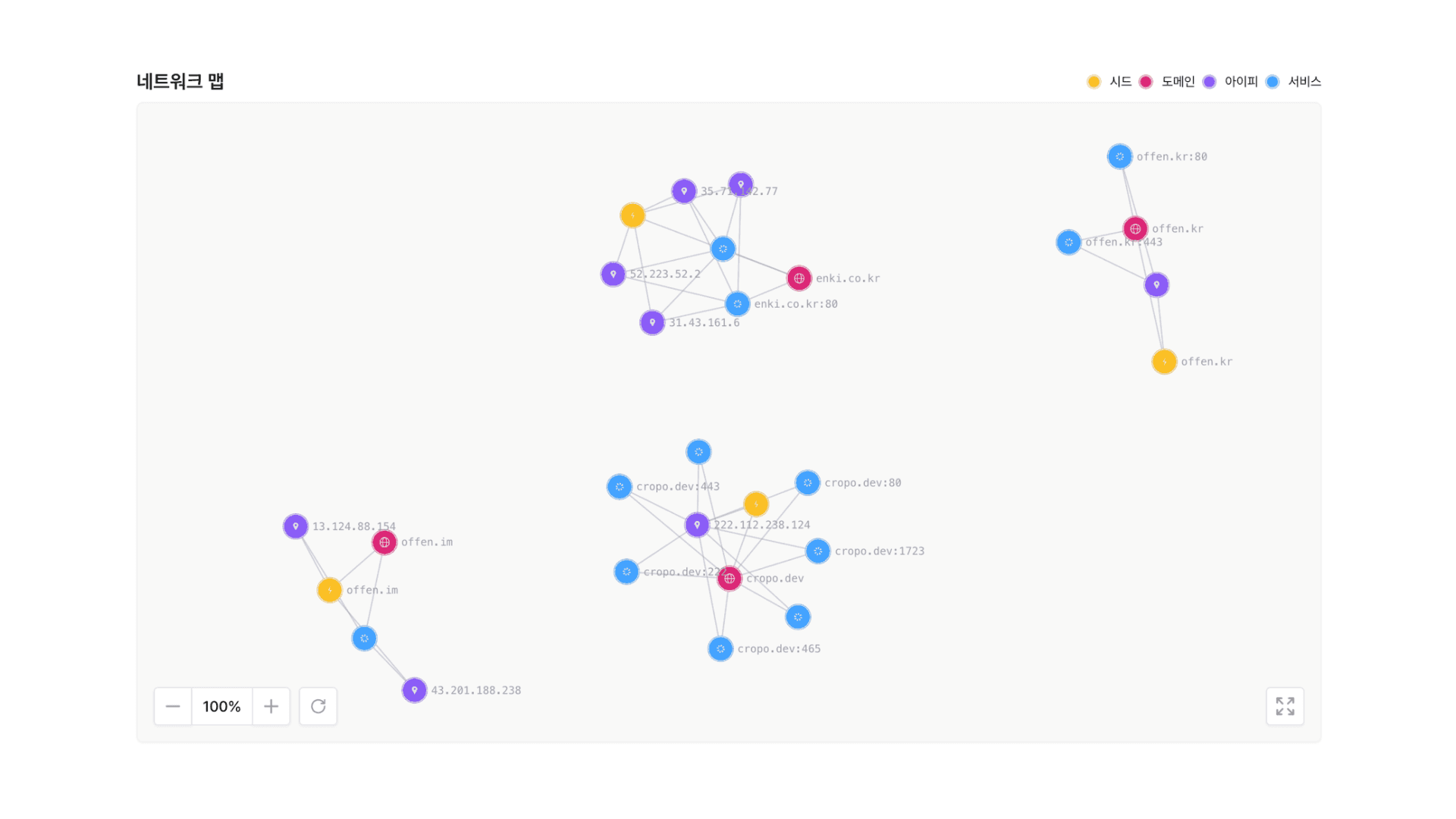
It presents the connection relationships among domains, IPs, and ports as intuitive graphics instead of complex text. See the security status at a glance. When a specific asset is breached, you can immediately understand through a network map how its impact could spread to core systems along which paths. When you need to report the status of your assets to executives, you can convey the situation with just one network map, without lengthy explanation.
OFFen ASM+ Pentesting (PTaaS) Synergy
Will the identified vulnerable asset actually be breached? How far could the impact spread?
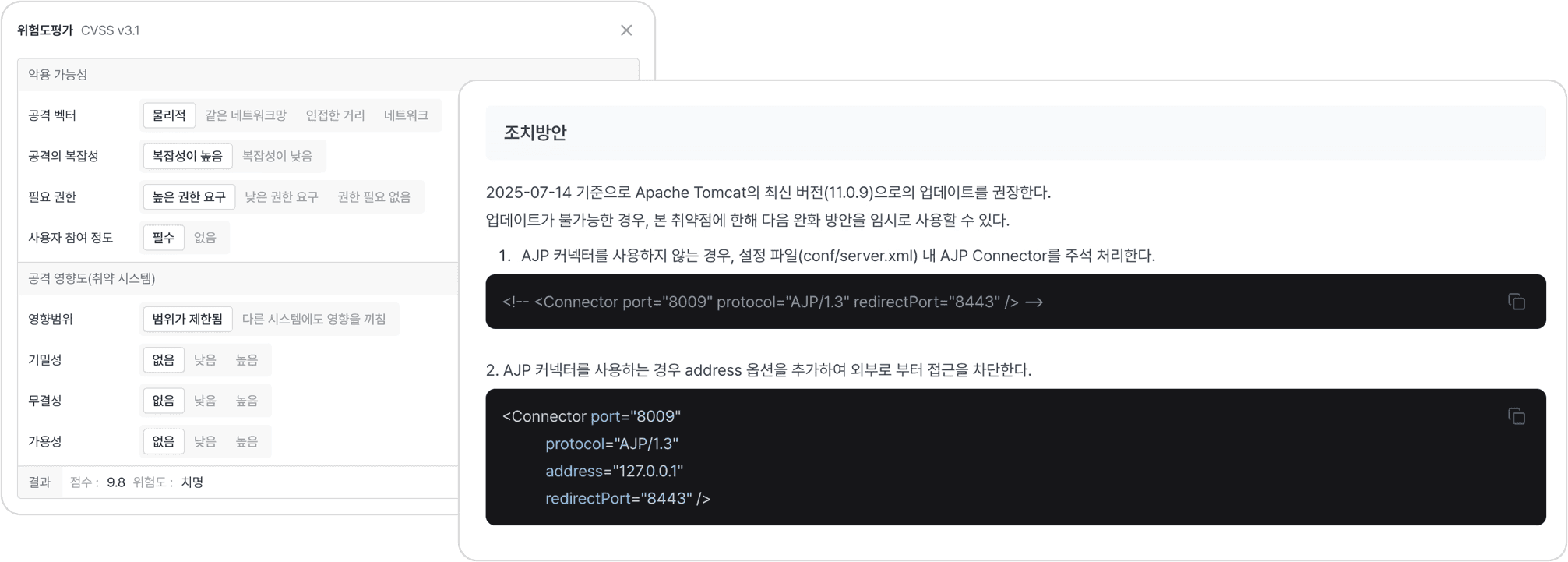
On the OFFen platform, you can request penetration testing as a service (PTaaS) from top 1% white hackers with a single click. Pentesters assess exploitability and attack impact, and each issue comes with a risk rating plus PoC and remediation guidance, so findings can lead straight to practical response.
From attack surface management to pentesting, OFFen
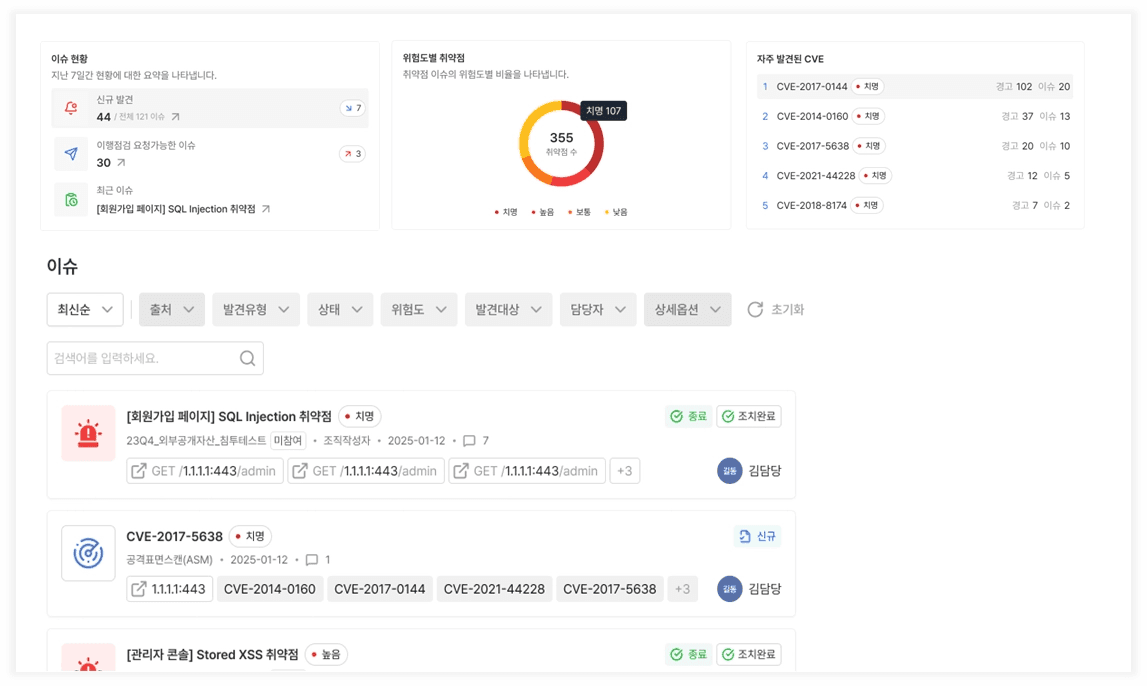
IT environments change every day. Tools used by different teams keep getting added, new servers go online, and new vulnerabilities are discovered. OFFen ASM continuously tracks domain change history and provides endpoint screenshots and tag summaries to quickly catch operational changes. Based on scan results, elite white hackers with championships from the world's most prestigious hacking competitions step in directly through OFFen PTaaS. Rather than merely listing vulnerabilities, it comprehensively validates the potential attack surface by assuming real damage scenarios for each asset based on selected externally exposed assets.
Change history tracking: Records domain changes and endpoint changes with real-time screenshots so operational changes are never missed.
Action-Plan included: White hackers with wins in world hacking defense competitions assume real damage scenarios and directly propose a CVE reproduction report and tailored remediation strategy.
No more budget worries for SMEs! Get government support with the '2026 Cloud Voucher'
Have you hesitated because of the cost of pentesting and attack surface management?
It may have seemed expensive, and you may not have known where or how to start.
Enki WhiteHat is participating as a supplier for the Ministry of Science and ICT's '2026 Cloud Voucher,' recognized for its technological capabilities, including GS Certification Level 1 and several security patents, as proved by its technology.
Item | Details |
|---|---|
Application period for demand companies | 2026.04.03 ~ 04.21 (※ May close early if there is a high volume of applicants) |
Project name | Cloud Service Distribution and Expansion Project |
Eligibility | SMEs nationwide (both existing Enki WhiteHat customers and new customers may apply) |
Support benefits | 80% support for OFFen usage fees, up to KRW 69.1 million |
How to apply | Submit a demand company application form at cloudsup.or.kr |
🙋 Dedicated 1:1 consultant support
From checking whether you can be selected as a cloud voucher demand company to preparing the usage plan, a dedicated manager will guide you directly.
If you are interested, please leave your inquiry below.
Why you need to respond with OFFen now
Even SMEs with limited security staff can achieve enterprise-level security posture through 'IT asset scan automation' and 'expert verification'.
First, preventing security incidents must be done as quickly as possible. In line with government policy direction, attack surface management and real-world penetration testing are becoming basic requirements, not optional ones. Security is not an area that ends with a one-time inspection; it is closer to a process of continuously checking and verifying status. Especially if you have never checked your current state based on externally exposed assets, that alone means it is time to review it at least once.
Second, it is an opportunity to receive vulnerability assessments from ENKI white hackers at the most reasonable price ever. For SMEs, channels to access PTaaS, where DEF CON award-winning white hackers with the No. 1 share in operating hacking defense competitions are directly deployed, are extremely rare.
Third, the attack surface management and penetration testing solution is discounted by 80%. If selected as a 2026 Cloud Voucher recipient, you only need to bear 20% of the total cost. (Government support of up to KRW 69.1 million)
Please experience ENKI WhiteHat's attack surface management service, proven in large enterprises and financial institutions, at an economical cost throughout 2026. A white-hacker group with rich hands-on experience will be a strong partner in eliminating your company's security blind spots.

Popular Articles